If you’re in the Department of Defense supply chain, you know that there are new cyber security requirements coming down the pipe with Cybersecurity Maturity Model Certification (CMMC). In November 2021, a new 2.0 version was released.
While the new version is intended to simplify requirements and the compliance process for small to medium-sized businesses, it’s still a big job for suppliers to get their arms around exactly what they need to do and when.
That’s where a Registered Practitioner (RP) comes in.
Look to a CMMC Registered Practitioner (RP) to get the consulting you need to untangle all the jargon, figure out what you need to do, and save on future CMMC assessment costs at the same time.
Here’s how a Registered Practitioner can help you to become CMMC compliant:
- Interpret CMMC Requirements
- Scoping (and Simplifying) the Extent of Compliance
- Perform a Gap Analysis
- Create a Remediation Plan
- Prepare Evidences for Security Control Implementation
1. Interpret CMMC Requirements
If you’re at Level 1, compliance doesn’t look so hard because you only need to comply with 17 practices from NIST 800-171.
Most companies, however, are going to ultimately need to certify at Level 2 which includes 100 practices from NIST 800-171. At that level, you must have the security controls in place, and documentation that includes tangible evidence along with it.
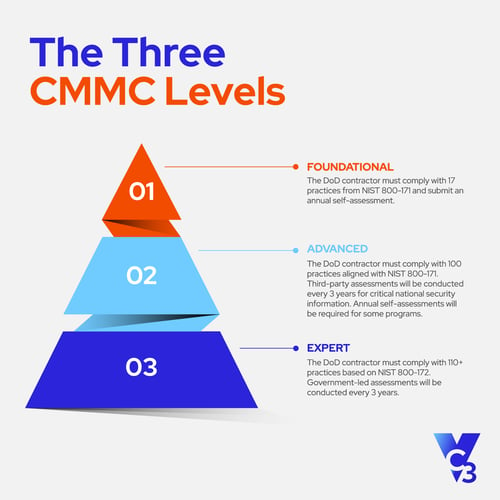
The official CMMC documentation for Level 2 is hundreds of pages long and includes 130 separate practices and processes that need attention. That’s a lot! Additionally, about half are technical and the other half are concerned with data access policies.
Unless they have experience with security compliance, it’s unrealistic to expect your IT and HR managers to be able to create a compliance plan on their own. A Registered Practitioner (RP) is trained to translate CMMC standards into security controls. An RP saves your team time, frustration, and work by providing guidance and recommendations.
2. Scoping (and Simplifying) the Extent of Compliance
The first thing you need to do to comply with CMMC is to determine exactly what data you need to protect and where it’s stored on your network.
Your entire network may not need to follow CMMC standards, only that piece that stores and transmits Controlled Unclassified Data (CUI), Federal Contract Information (FCI), and technical data. -- Your contract should tell you what you have.
A Registered Practitioner can help you figure out how this data flows through your organization and give you recommendations for how you can segment your network, and modify processes so that the DoD data doesn’t touch anything else.
Narrowing down the scope of CMMC standards to exclusively apply to the controlled data will also help you to save on assessment costs if you’re required to undergo a third-party audit.
3. Perform a Gap Analysis
After you’ve figured out what data you’re protecting and where it’s stored, you need to see what security practices are already in place that can be applied to compliance, and where you fall short. A Registered Practitioner can do a Gap Analysis to reveal that information.
An RP will go through the CMMC controls one by one to get a yes or a no. If the answer is “yes”, the RP will then look to see if you have evidence for the control. Any “no” answers will go to a list for remediation. Some of the work for the Gap Analysis can be done remotely, but the RP will also need to visit your physical site.
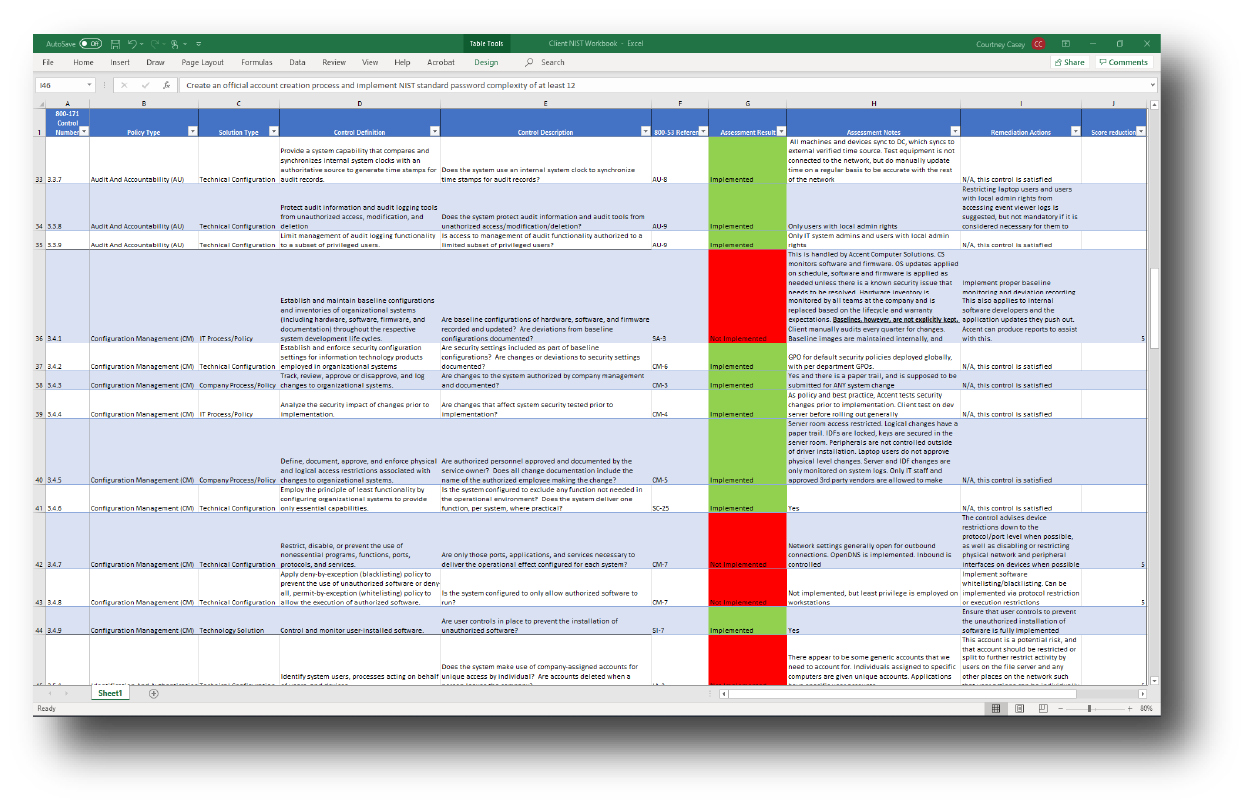 NIST Gap Analysis Discovery Example
NIST Gap Analysis Discovery Example
It’s very important that you get a Gap Analysis done as soon as you know that you need to comply with CMMC because it will give you a clear picture of what you need to do to attain compliance. Depending on your situation, you may need to invest in hardware or software, as well as get ongoing management tasks in place. You’ll need time to train your people to follow your non-technical policies.
You also must show that compliance has been in place for a period of time.
4. Create a Remediation Plan
When you’re done with your Gap Analysis, you’re going to end up with a list of controls that you need to implement. These aren’t always clear-cut. If you need additional technical measures, a Registered Practitioner (RP) can help you identify the technologies that will be compatible with your IT environment.
When it comes to security policies, an RP can save you a lot of time by guiding you to templates that you can customize, and provide recommendations for training and enforcement.
Compliance isn’t just a matter of passing an audit or submitting documentation, but in setting up processes and practices that provide ongoing security, so the list of recommendations that an RP gives you will be made with long-term management in mind.
Additionally, CMMC 2.0 allows contractors to submit a Plan of Action and Milestones (POAM) when they can’t totally comply with requirements to illustrate due diligence in moving towards complete compliance.
5. Prepare Evidences for Security Control Implementation
Preparing documentation for a self-assessment or third-party audit means that you not only have to have the controls in place, but you also have to verify them.
For example, if you are restricting access to a place on your network you could have a screenshot of the policy in place on the server, and an interview with someone who is responsible for enforcing that policy.
A Registered Practitioner can help you to identify appropriate evidences and organize them so that when you have your audit, they’re easily accessible.
CMMC Consulting
VC3 is a Registered Practitioner Organization (RPO) and provides CMMC consulting through the services of on-staff Registered Practitioners. We can help you create a path to CMMC compliance so that you can continue to be a valued DoD supplier.
Note: This article was originally published in February 2021. It was updated in December 2021 to reflect CMMC 2.0 standards.





